In my opinion there are too many agents and too many replicas need. If you keep in mind, that every 4 hours new Definition Update are released, then you see, that all the process need to be aligned very well.
In this case we use a PowerShell script to handle the Download of the new definitions. Then we use the Package and Program replications to DP’s and finally I use the UNC integration from the EP-Policy.
Here we go with the Step-by-Step integration:
Andre Picker has written a PowerShell Script to download the Definition Files:
https://gallery.technet.microsoft.com/SCEP-Definition-Updates-to-fde57ebf
Here I have an updated Version of it:
https://github.com/slaet/SCCM_Scripts/blob/master/downloadscepupdates.ps1
The Only thing you need to modify in the Script is the Path for the Download location
| # Define the target path | |
| ################################################################################## | |
| $pathx86 = “C:\Temp\SchedTask\SCEPupdates\x86\” | |
| $pathx64 = “C:\Temp\SchedTask\SCEPupdates\x64\” |
For the Script create a new Folder where the Script can be placed, to add them later to the Scheduled Tasks.
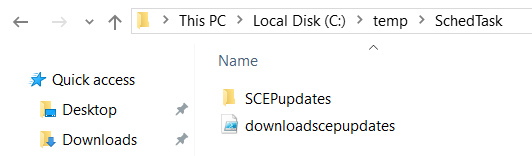
You should also create a Folder in the same or a different location for the files that should be downloaded.
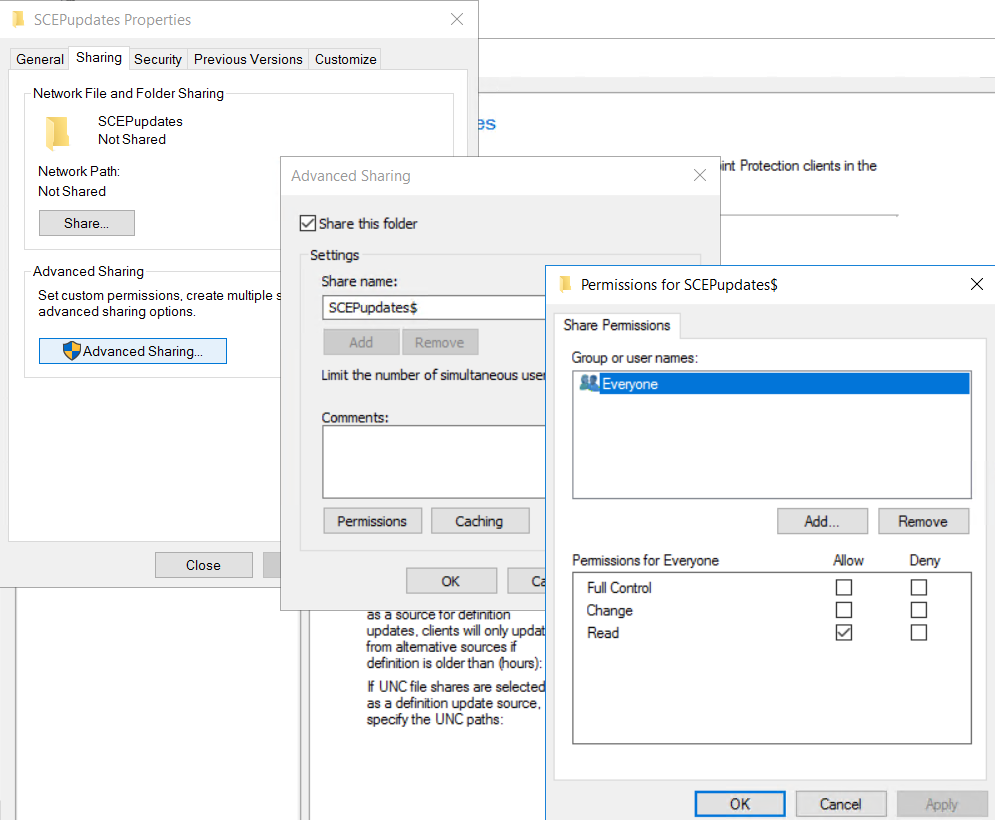
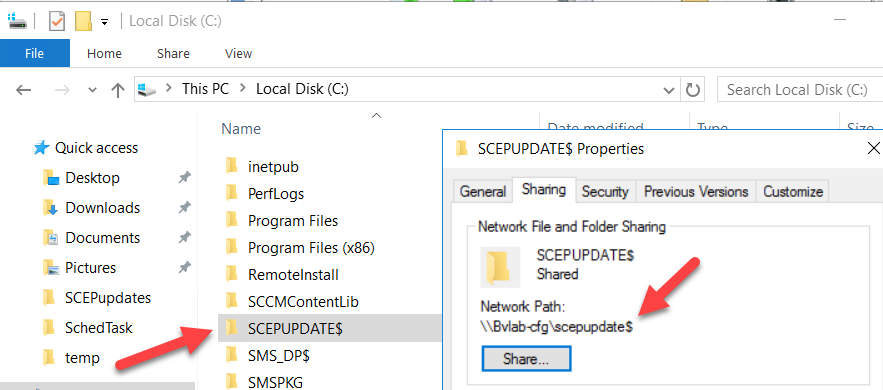
For that Folder, we need also a Share, I just use the Folder name with a $, also hold the default Permissions, like everyone; read.
Now we can go to the Scheduled Task Manager and Add a Task:
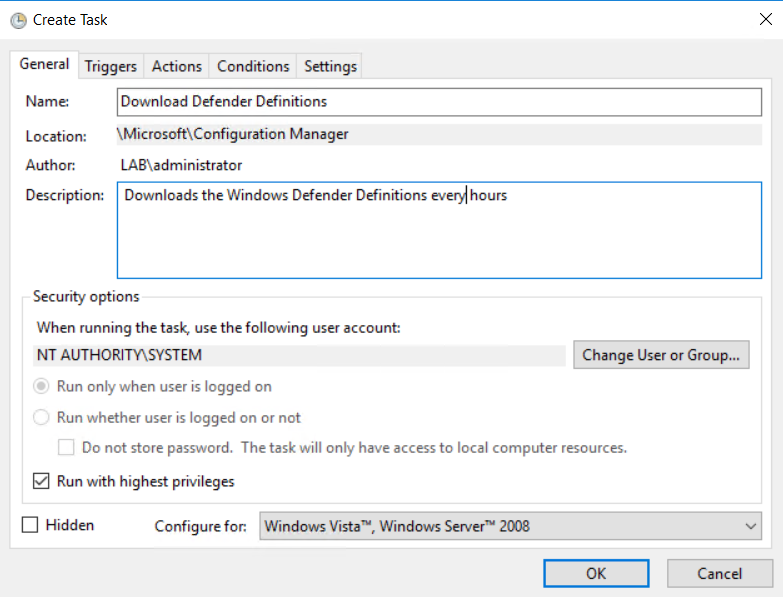
It needs to be running as System
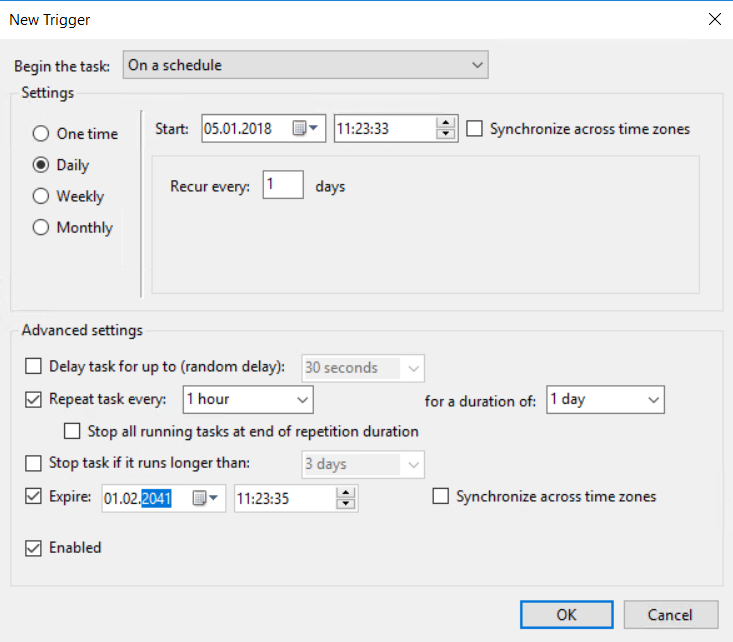
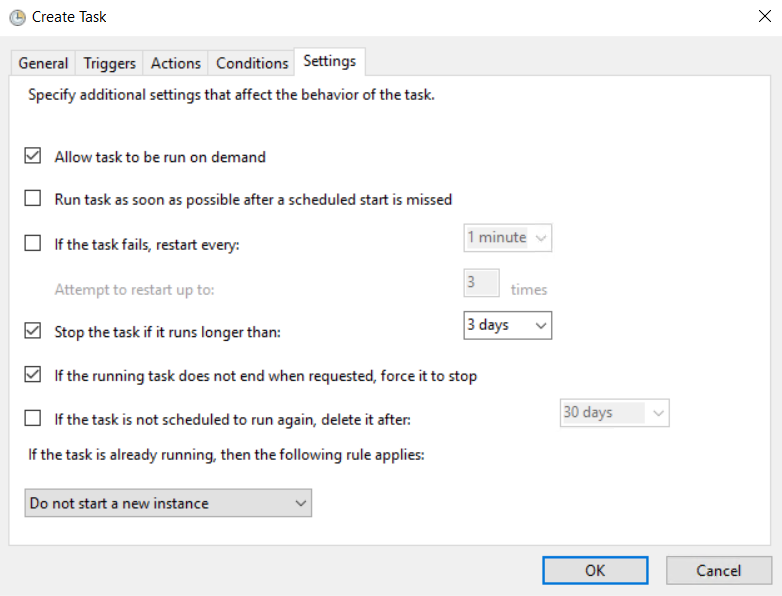
Run the Task every Hour, and every Day
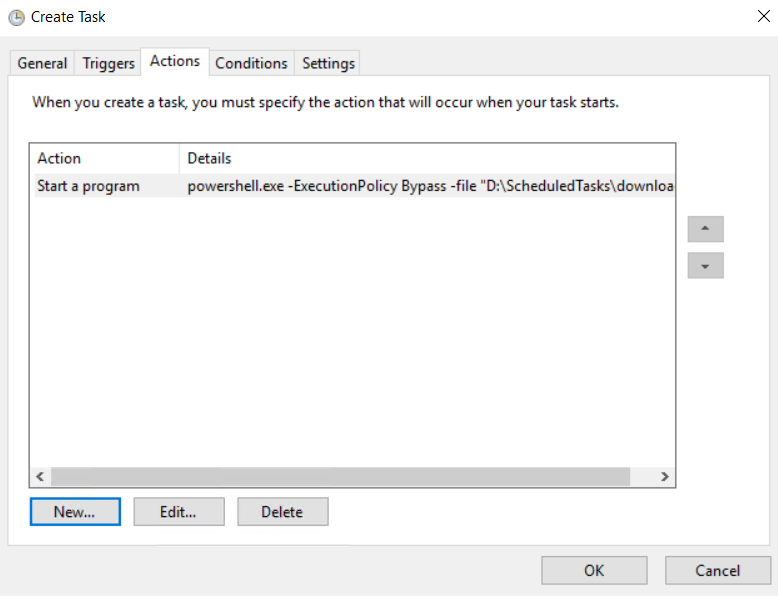
Add the Action with
Poweshell.exe
and the Command
-ExecutionPolicy Bypass -file “C:\temp\SchedTask\downloadscepupdates.ps1”
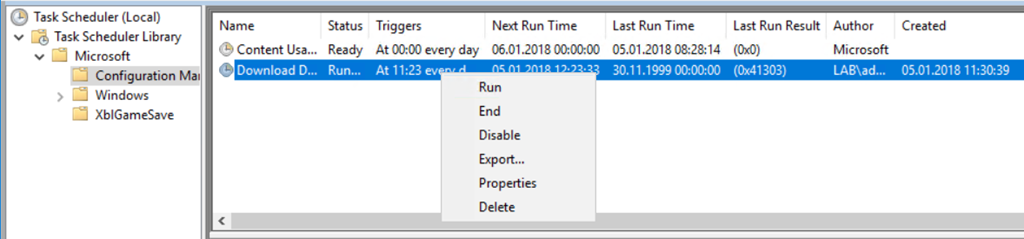
For testing, you can run it the first time manually, to see that the files can be downloaded in the two folders (it can take a little while).
![]()
I have exported the XML, you can download it here:
https://github.com/slaet/SCCM_Scripts/blob/master/Download%20Defender%20Definitions.xml
And just add/import it to your Scheduled Task, control any setting and run it for testing.
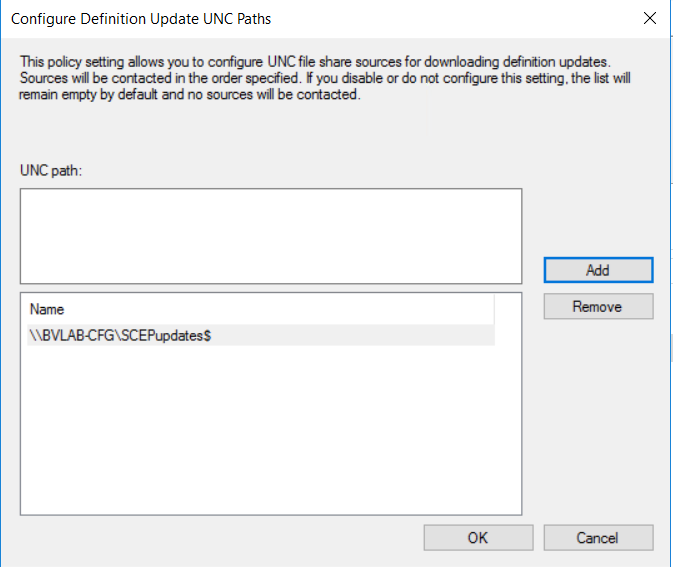
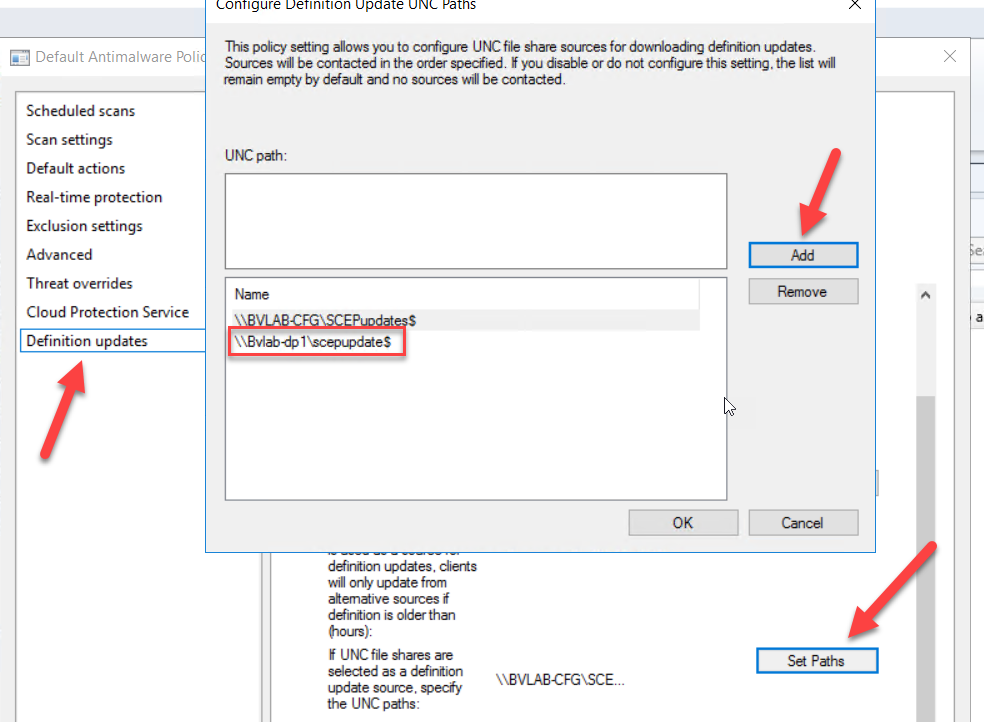
As next we go to the Antimalware Policy and change the order for the Sources. I just set the UNC Path as first option, as the second ConfigMgr and third MS Update and Microsoft Malware Protection Center. The last option is needed to protect the clients in the internet.
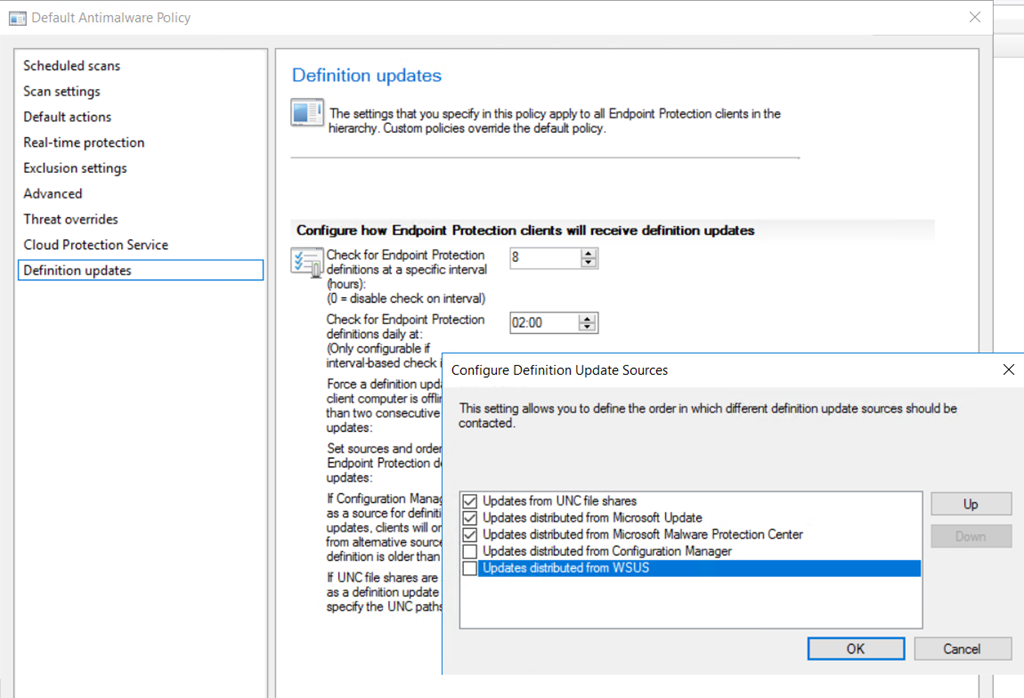
In addition I need to add the path to the share I created. It is the root folder, the client can handle the x86 and x64 Folder by himself.
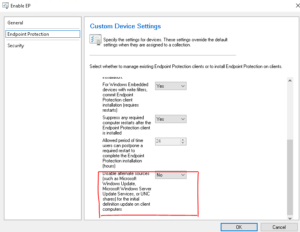
Do not Forget to enable the UNC in the Client Settings:
This Step by Step is for a single Primary Site with no DP’s and no Branch-Cache or any bigger network with different Location.
If you would like to Implement that in a “Big” Environment with multi DP’s then you can add A Packages with no Program, and replicate it to all DP’s, use the Share integration from the Package and Just change or add the UNC Path’s, or maybe add a new Antimalware Policy with separate paths to the different UNC Shares and Deploy them to the right collections, that clients in separate Collections just use the correct path.
Here are the steps to create the Package:
The Creation of the Package is simple, just add the UNC Path to the sources root folder
and create the Package without a Program.
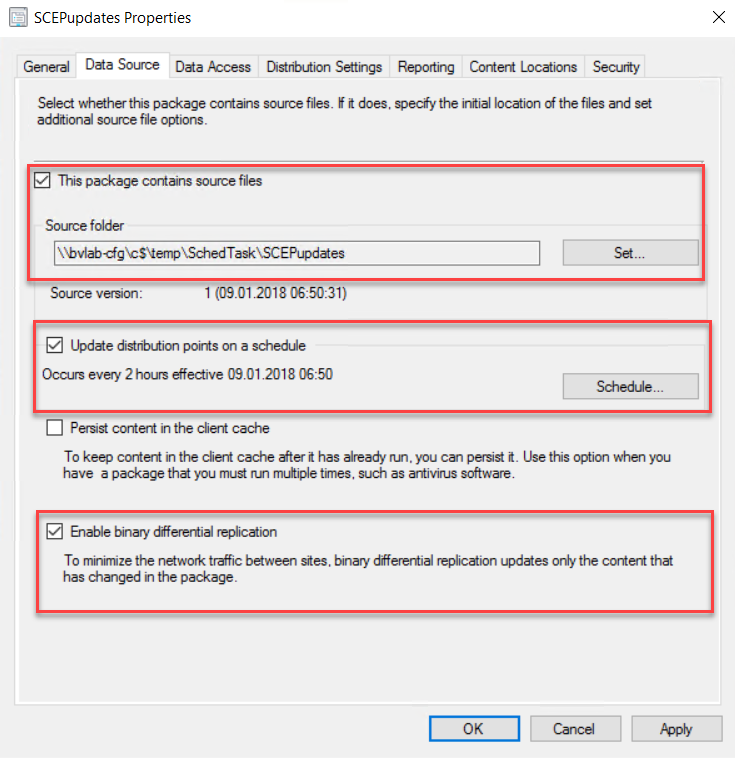
Then go to Properties of the Package and modify in the Data source tab the automatic update to every 2 hours and also enable the differential replication.
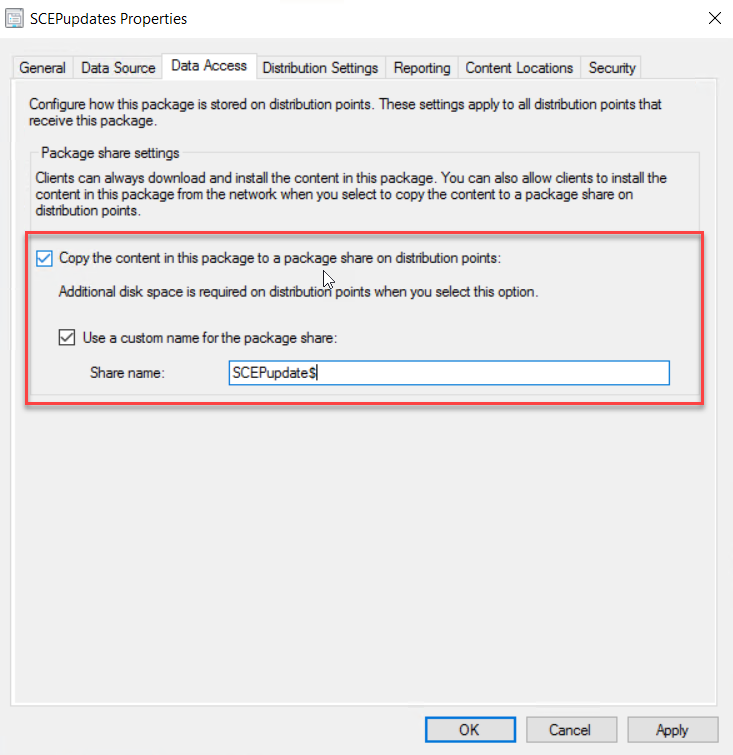
In the Data Access Tab enable the copy content in this package to a share on the distribution point.
This will end up as a Folder that is shared in the Root of the DP
Now you can use that share to add them in the Antimalware Policy as an additional source location
That’s it…
Hope it helps and saves you some time to enjoy a beer 🙂, this Post is as is, test it first and do your test in a LAB before implementing it to Production.
Have a Wonderful Day
Here is also another cool solution to do updates during the Tasksequence in Config Manager or MDT, thank you Jörgen for Sharing.
Leave a Reply